Every organization that has granted a vendor system the right to act on its behalf has made a trust decision. Most have made that decision once, at procurement, embedded in a contract and a technical onboarding process, and have not revisited it since. The system gets credentialed, integrated, and given the access it needs to function. From that point forward, it acts. It pushes updates. It executes instructions. It touches endpoints, pipelines, credentials, and production systems, often without human review of individual actions, because that is precisely the operational efficiency it was purchased to deliver.
That is not a criticism of how organizations procure technology. Delegated authority is how modern infrastructure operates at scale. The question is not whether to delegate, it is whether the organization has built a corresponding model for what happens when that delegation needs to be constrained, adjusted, or revoked. In most organizations, that model does not exist in any form that would be recognizable to the board or the executive team. It may exist in the institutional knowledge of the people who manage the systems. It almost certainly does not exist as a defined governance capability with tested procedures and clear decision rights.
That absence is not an IT gap. It is a governance gap, and it carries capital consequences. Delegated authority without a revocation model is not governance. It is exposure.
The Pattern the Incidents Confirm
The last several years have produced a set of high-visibility failures that look different on the surface but expose the same structural absence underneath. A management platform pushes a malicious payload. A security tool misidentifies legitimate files and quarantines them at scale. An endpoint agent takes down production systems following a flawed update. A pipeline tool executes compromised code after a prior breach left credentials only partially rotated.
CrowdStrike, Kaseya, Webroot, Aqua Security’s Trivy: the causes varied, and in not every case was the failure malicious. What they share is the organizational experience that follows: a trusted system has moved outside its intended bounds, it is still acting with the authority it was granted, and the organization does not have a clear model for how to respond. Teams pull runbooks, security leads convene, and postmortems are scheduled. The harder question, however, “What is our actual authority model, and how do we adjust it right now,” rarely has a pre-built answer.
The instinct is to treat each incident as its own category. Build a CrowdStrike playbook. Update the vendor review checklist. That work is not useless, but it addresses the symptom while leaving the structural condition untouched. The next incident will not resemble the last one in its mechanics. It will resemble it exactly in the governance gap it exposes.
Why Incident Response Is Not the Same Investment
There is a meaningful distinction between incident preparedness and governance preparedness, and most organizations have invested heavily in the former while leaving the latter largely unexamined.
Incident response is a forensic and operational capability. It answers what happened, sequences the containment steps, and drives the recovery workflow. Done well, it is valuable. Though it is also, by definition, reactive. Response engages after a system has already acted in ways the organization did not intend.
Governance preparedness is prior to that. It answers the questions that make incident response faster and more decisive: what authority have we actually granted, to which systems, under what assumptions? What conditions would require us to treat a vendor issue not as a service disruption but as a control-plane event requiring a different class of response? How quickly can we act, and who has the authority to authorize that action?
These are not technical questions. They are decisions about how the organization is structured to act under uncertainty. The fact that they live primarily in technical teams, to the extent they are answered at all, is itself a governance signal. A board that has visibility into vendor concentration risk but no visibility into vendor authority exposure is operating with an incomplete picture of the organization’s actual risk posture. The gap between those two is where incidents become crises.
The Four Questions Governance Must Answer
The governance work is not abstract. It resolves into four concrete questions, each of which, left unanswered, represents a defined category of organizational exposure.
The first is an inventory question: which systems hold delegated authority, and at what scope? Not which vendors are under contract, and not which tools appear in the asset register. Which systems have active credentials, active permissions, and the operational capacity to act on the organization’s behalf across meaningful infrastructure? This inventory is rarely maintained at the governance level. It tends to exist in the minds of the people who manage it, which means it is both incomplete and inaccessible at the moment it is most needed. An organization that cannot answer this question at the board level has delegated authority without retaining visibility over what it has delegated.
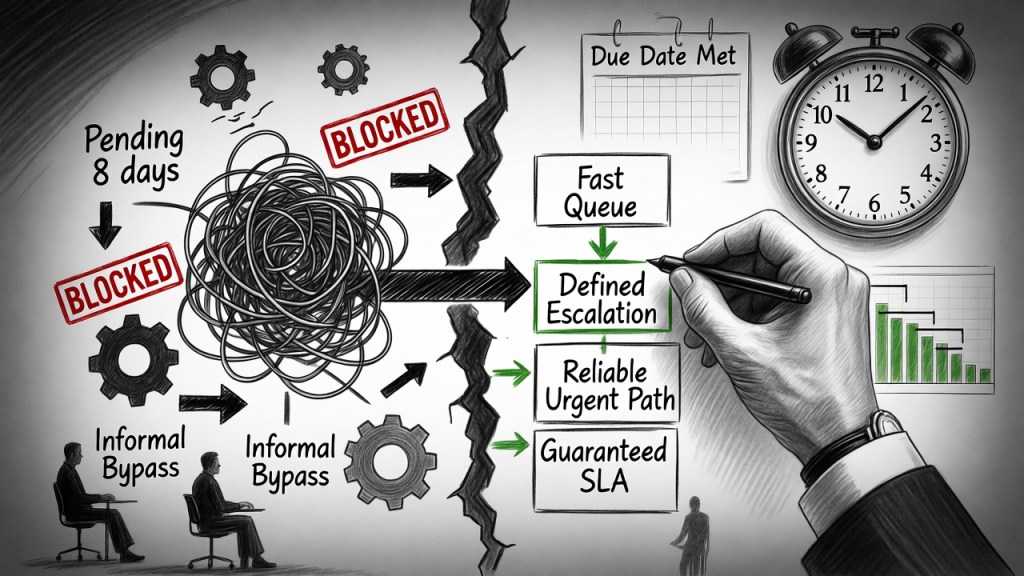
The second is a classification question: what threshold defines a vendor issue as a control-plane event? Not every vendor incident warrants the same response. A service degradation is a continuity problem. A system operating beyond its expected behavior, while still holding delegated authority, is a different category entirely, one that may require constraining or revoking authority before the scope of impact is fully understood. Without a pre-defined threshold, that decision gets made in real time, under pressure, by people who have never been asked to think about it before.
The third is an assumption question: what does the organization assume about credential exposure and downstream impact when a trusted system is compromised? Breaches of vendor systems rarely stay contained to the immediate point of failure. A system with broad access has broad exposure. And if a management platform is compromised, the question is not only what that platform did, but what else it could reach, what credentials it held, and what lateral exposure exists. Organizations that have not mapped these dependencies before an incident find themselves building that map during one.
The fourth is a capability question: how quickly can delegated authority be constrained or revoked, and has that capability ever been tested under realistic conditions? An organization may have documented procedures for revoking vendor access. Those procedures may work cleanly in a controlled test. They may not work at speed, under pressure, with the actual systems involved, in the middle of an active incident. The gap between the theoretical capability and the demonstrated capability is where the board’s risk posture shifts from real to nominal. That gap is only visible if someone has thought to close it before it matters.
The PE Context
In private equity environments, these questions carry additional weight because unresolved governance gaps are amplified by time compression. A portfolio company managing a vendor authority incident without a pre-defined revocation model does not simply face operational disruption, it faces decision paralysis at the moment when speed is the primary determinant of outcome. Leadership teams that have never been asked to answer these questions before a failure spend their recovery window discovering what they don’t know. That is a value destruction scenario, and it belongs in the operating partner’s diligence framework accordingly.
Governance as a Structural Asset
The argument here is not that vendor systems should be trusted less. It is that trust extended without a revocation model is not a governance posture, it is an assumption, and assumptions are not assets.
Organizations that have answered these four questions before a failure have built something real: the capacity to move from uncertainty back to control with speed and confidence. They know what they have delegated. They know what constitutes a threshold event. They know what their exposure map looks like. And they know whether their revocation capability is real or theoretical. When a trusted system moves outside its intended bounds, that preparation compresses the time between recognition and response.
Organizations that have not answered these questions are dependent on something else: the composure, competence, and institutional knowledge of whoever happens to be in the room when the incident begins. That is not a governance model. It is a concentration of judgment in individuals rather than in structure. And as with every other form of key-person dependency, it holds until it doesn’t.
Governance over delegated authority is a structural asset. Like any asset, it requires deliberate investment, periodic review, and protection against erosion. The incidents that make headlines are not the argument for that investment. They are the evidence that the argument was always correct.